 This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we look at ways to prevent malware attacks on your devices using Antispyware, Antivirus, and Firewall Software.
This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we look at ways to prevent malware attacks on your devices using Antispyware, Antivirus, and Firewall Software.
Please also review our WordPress Security Guide For Beginners and our free WordPress Security Checklist.
***
Software Security – Preventing Malware Attacks
If you plan to do anything online, then you must accept the fact that Malware is not going to go away, and that new forms of malware are simply going to keep surfacing on a regular basis.
The two main ways of dealing with malware are:
- Stay informed and up-to-date
- Secure your computer against viruses, spyware, and malware.
Staying Up-To-Date
If you are interested in staying up-to-date with the latest malware threats, you can visit threat update pages from reputable security companies like the ones listed below:
Securing Your Computer
Making sure that your computer is free of spyware, malware, and virus infections is vitally important to your online security. There’s no point securing your WordPress site if a keylogger is installed on your computer and can send your password and login details to hackers.
Antispyware / AntiVirus Protection
Anti-spyware programs combat spyware by providing real-time protection, scanning, and removal of any spyware software found on your computer. Antivirus software performs a similar function, but it looks instead for viruses, worms, and trojans, mostly sent to you via email.
![]()
Tip: Make sure that any antispyware programs you install on your computer are authentic. Unfortunately, some programs marketed as free spyware detectors will actually install spyware on your computer. It’s best to stick with antispyware software from reputable and trusted manufacturers.
Below are some of the most widely-used and trusted computer protection software programs available to help keep your computer free of malware, spyware, viruses, etc…
Some of the programs listed below are available as a standalone software package, and others are available as part of an integrated security solution. Many security companies offer free or trial versions of their products
![]()
We recommend investing in a reliable commercial antispyware/antivirus program for maximum protection against malware and to prevent and eliminate spyware and viruses from infecting your computer system.
Microsoft Security Essentials
Microsoft Windows has a free security program called Microsoft Security Essentials that works in the background to protect your PC. It checks for updates automatically a few times a day and doesn’t slow your PC down while it works …

The program is easy to use and allows you to see if your computer is secure from threats using a very simple system – if the icon next to your computer clock is green, everything’s good; if it’s red, then something is wrong and needs immediate attention …

Clicking on the icon will then open up an alert window notifying you of the problem, and giving you options to fix the issue or potential threat …

Microsoft Security Essentials is available as a free download …

To download this software program, visit the site below:
Lavasoft’s Ad-Aware
Ad-Aware is one of the world’s most downloaded security software programs. It immediately detects malware before it harms your PC, scans your download files before they have a chance to inflict damage, and automatically protects your computer from the latest threats and the newest malware being distributed through bad URLs and malicious websites.
Ad-Aware is available in different versions (see below).
To learn more about the Ad-Aware software products, visit the sites below:
Spybot Search & Destroy
Spybot Search & Destroy is a free and constantly updated antispyware utility that targets adware, malicious code, and other threats. Spybot isn’t a replacement for a full antivirus program, but it can detect and remove a multitude of adware files and modules from your computer and remove some other threats.
You can use the adware and malware scanner to regularly check your system. Spybot has been around for years, and so offers users plenty of resources like tutorials, FAQs, how-tos, forums, etc.
To learn more about the Spybot software product, visit the site below:
Malwarebytes
Malwarebytes Anti-Malware software uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more. There is also a Malwarebytes Anti-Malware PRO version that provides constant protection and helps to automatically prevent malware from reinfecting your PC.
To learn more about Malwarebytes, visit the site below:
Avast
Avast is one of the most downloaded and highly recommended Antivirus programs available. It’s a complete security tool that protects you from all threats – Internet, email, local files, peer-to-peer (P2P) connections, instant messages, and more. Avast also has a “heuristics engine” that can detect previously unknown viruses and other malware.
To learn more about Avast security software, visit the site below:
Kaspersky Lab
Kaspersky Lab is one of the fastest growing security companies in the world and has a mission to provide the world’s most effective, responsive and efficient protection against cyber-threats for all online users. Free virus scans and free trials of security products are available from the Kaspersky site
To learn more about Kaspersky security products, visit the site below:
BitDefender
Bitdefender provides a range of security software solutions that are easy to set up and configure. The Bitdefender Antivirus Free Edition program uses very little system resources, so it won’t slow down your computer. It also provides constant virus protection (also called on-access or resident protection) for free, which makes it a viable alternative to paid solutions from companies that charge for their software and for yearly access to updates (e.g. McAfee, Norton, etc…).
To learn more about Bitdefender security products, visit the site below:
Norton By Symantec
Symantec’s Norton range of software products provides comprehensive security protection for computers (and mobile devices). Norton products are available as standalone packages or as a ‘one-in-all’ security solution. For example, Norton 360 is easy to install and provides complete computer security by integrating antispyware, antivirus, and firewall protection …

To learn more about Symantec’s range of security products, visit the site below:
AVG Antivirus
AntiVirus Free from AVG provides a comprehensive antivirus and antispyware solution that also includes an email scanner, link scanner, scheduled scanning options, automatic updates, and more.
AVG is considered by many to be one of the best free antivirus programs available today. It is a set-and-forget software program that is frequently updated and includes many premium features.
To learn more about the AVG security software, visit the site below:
McAfee
McAfee provides comprehensive protection for home and office computers, and cost-effective security solutions for businesses.
To learn more about McAfee security products, visit the site below:
Trend Micro
Trend Micro Antivirus software provides protection against malware attacks and offers accurate phishing and spam protection, plus and a firewall booster that can block exploit attacks.
To learn more about Trend Micro, visit the site below:
![]()
If you are interested in comparing how different antivirus software programs perform, the AV-TEST Institute is a leading international and independent service provider in the fields of IT security and anti-virus research. They independently examine free and paid antivirus programs and rank them for protection, repair, and usability. …

As antivirus programs are regularly updated, AV-TEST updates the latest test results every few months.
To view detailed test reports for antivirus programs, visit the AV-TEST site below:
Firewall Protection
Firewalls are an important part of your overall online security strategy. A Firewall analyzes traffic data (known as ‘packets’) before it is allowed into your computer and makes sure that it is not malware.
A firewall is like a security guard standing outside a busy nightclub. Its main job is to check everyone coming in while also keeping any undesirables out.
To learn more about using firewalls, see the relevant section in the tutorial below:
Below we have listed a number of software-based firewall programs you may want to look into for protecting your computer from external attacks. Most simple two-way firewalls ask you to allow or deny Internet access to unknown programs. Many automatically allow trustworthy apps and remember your decisions to become silent over time.
Windows Firewall
Microsoft Windows comes with a built-in firewall program. We recommend choosing an alternative firewall solution, however, as these tend to offer easier control of outbound protection and additional features.
![]()
If you plan to install a third-party firewall solution, make sure to disable the Microsoft Firewall first, as having two firewalls running simultaneously will create problems.
To do this, click on the ‘Start’ button (the Windows icon located on the bottom left-hand corner of your screen) …

Choose ‘Control Panel’ …

Click on ‘System and Security’ …

Click on ‘Windows Firewall’ (or ‘Check firewall status’) …

From the menu, select ‘Turn Windows Firewall on or off’ …

Here you can turn Windows Firewall on, or off (not recommended unless you are installing a third-party firewall program) …

Note: Some security programs will override your system’s default settings to prevent conflicts from happening. Depending on the security product you have installed, you should see a notification that your security settings are being managed or overridden by the program you have installed …

Norton By Symantec
We covered the Norton security products earlier. As well as antivirus protection, Norton products also provide a Firewall program.
To learn more about Symantec’s range of security products, visit the site below:
Comodo
Comodo is a robust firewall software solution that consistently scores highly in security tests and security expert reviews.
Comodo includes a “memory firewall” (protects against buffer overflow attacks) and a “sandbox” component that limits unknown applications and new software installations from affecting your computer. If an unknown application attempts to enter your computer via the firewall, Comodo will deny the application and ask you what to do. Comodo’s firewall software application for Windows is available as a free download.
To learn more about Comodo Firewall, visit the site below:
ZoneAlarm
ZoneAlarm is a simple and user-friendly firewall application. ZoneAlarm is currently installed on over 80 million computers and offers advanced firewall protection that monitors programs for suspicious behavior spotting and stopping new attacks that bypass traditional anti-virus protection.
ZoneAlarm offers a free download of the software with certain conditions (e.g. individual and not-for-profit use).
To learn more about ZoneAlarm, visit the site below:
PrivateFirewall
Private Firewall is a feature-packed firewall solution made available as unrestricted freeware. It provides a multi-layer security solution that includes behavior blocking technology, standard firewall protection, virus, spyware, and malware protection, process and application security, registry protection and more.
Additionally, there are many configurable settings, allowing you to set different security levels for Internet access and computer network security (ie. file and printer sharing) and configure different profiles (e.g. Home, Office, and Remote). Private Firewall is a very effective firewall program, but it is aimed primarily at slightly more advanced users.
To learn more about PrivateFirewall, visit the site below:
![]()
In addition to the products listed above, we recommend that you search online for user and technology reviews and do your own thorough research and due diligence before investing in a security software program.
![]()
As well as enabling firewalls on your computer and other devices in your network, you can also add a firewall to your WordPress site, using plugins.
You can search for WordPress Firewall plugins inside your WordPress dashboard (Plugins > Add New), or the WordPress Free Plugin Directory …
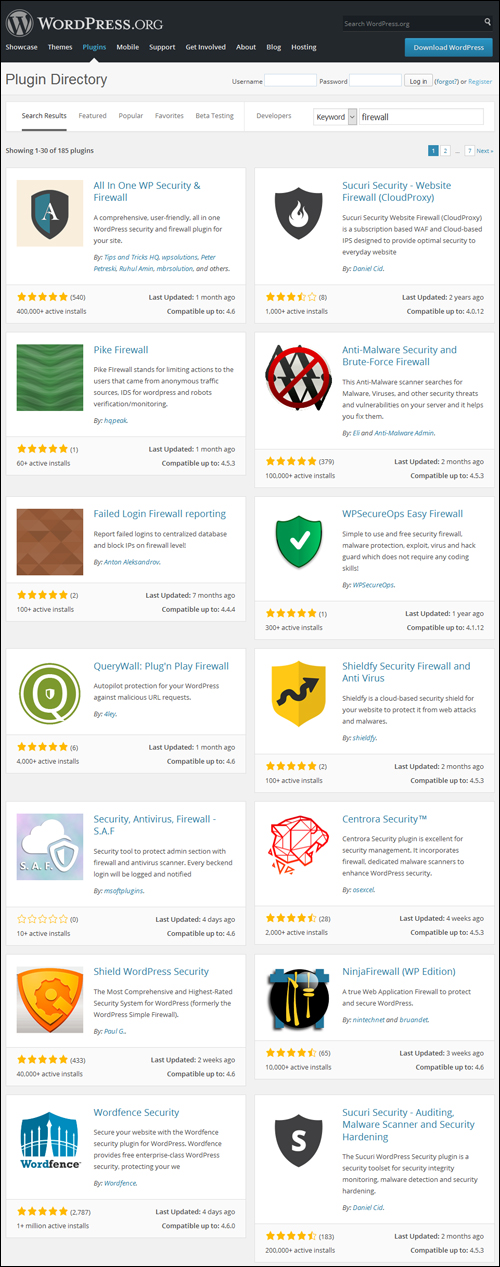
(WordPress Plugins – Firewall)
Search the WordPress Free Plugin Repository for firewall plugins below:
Next Step:
Now that we’ve looked at ways to prevent malware attacks on your devices, the next step is to review useful software security tips.
To review more software security tips, see the tutorial below:
See Also …
References

(Source: Pixabay)
***
"Wow! I never knew there's so much to learn about WordPress! I bought one of the WordPress for Dummies three years ago, such authors need to be on this course!" - Rich Law, Create A Blog Now
***












