This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we provide an overview of the security components that help to keep your WordPress site secure and protected and links to other tutorial modules in this series.
This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we provide an overview of the security components that help to keep your WordPress site secure and protected and links to other tutorial modules in this series.
***
WordPress Security Guide For Beginners
As we rely more and more each day on accessing electronic data from websites, online security has become a topic of extreme importance. This is especially true for website owners, who now live with the constant threat of having their websites attacked by hackers and malicious users.
According to security experts, online hacking activity is at an unprecedented level. Even sites that receive almost no visitors, or that have little to no visibility online can be subjected to hundreds of attacks a day from brute-force bots.
Ensuring that your WordPress site remains secure and protected against hackers, malicious bots, and unauthorized users is an essential part of having a functional and successful digital presence.
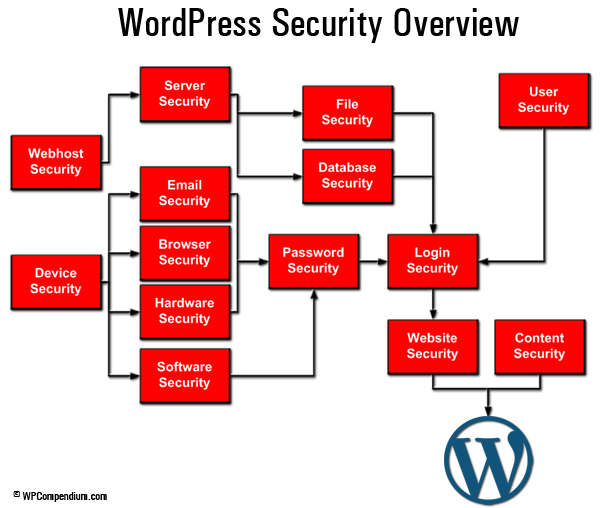
WordPress Security Overview
As you will learn in this guide, WordPress itself is a secure platform for publishing your website or blog. There are many other components, however, that can affect (and compromise) the security of your WordPress site …
(WordPress Security Overview – Click Image Above To Enlarge)
WordPress sites are prone to attack because WordPress is the most widely used CMS platform on the web. WordPress, therefore, is particularly attractive to hackers wanting to score a “big win” or to gain bragging rights and prestige among their peers.
Some of the biggest companies in the world using WordPress have been subjected to attacks. Many have had their sites hacked and compromised because of something as simple as running an ‘out-of-date’ version of WordPress.
Once a hacker finds a security weakness they can exploit in an older version of WordPress, they can quickly code ‘bots’ (automated software scripts) that will go out searching for other WordPress sites with the same vulnerabilities. If the bots find sites that have no security measures in place, hackers are then able to easily access site files and administration areas and do significant damage once they get inside.
How Hackers Gain Access To Websites
It’s important to understand that many hackers use very sophisticated methods to gain access and exploit unsecured and unprotected websites. Many websites are often compromised while remaining completely undetected by the site owner.
The screenshot below from BlogDefender.com, a company that provides WordPress security training and resources, shows how most people think hackers operate …

(Source: BlogDefender.com)
As BlogDefender.com’s Matt Garrett puts it, when most people think of hackers, they believe that some nerd living with his mother launches the odd attack on a WordPress site.
Matt then goes on to say that, in reality, how WordPress hacking actually works looks more like this …
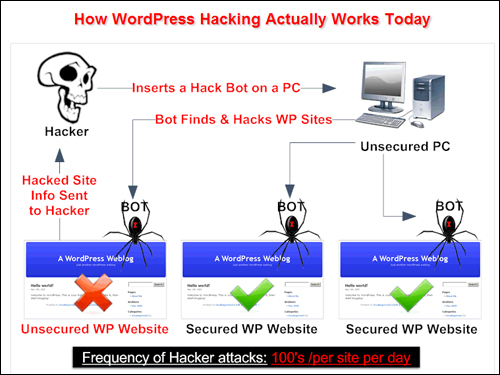
(Source: BlogDefender.com)
As you can see from the above, hackers (who are typically based in countries that have no laws or resources to prosecute them), write ‘bots’ which get implanted on a previously hacked PC or server. These bots then automatically search, find, and attack WordPress sites with multiple exploits & can continue doing so until they are switched off by the hackers themselves.
Additionally, many hackers work for organized criminal networks with significant financial backing and resources to fund elaborate scams and attacks, so the likelihood of downloading something (e.g. a free plugin or a free theme) from an infected site or from a compromised computer is very high.
Once a site is hacked, it can become an attack site that will then go on to infect many other devices with malware, or be used for other cybercriminal activities. This method of turning hacked computers into automated “hacking agents” allows bots to compromise thousands of sites per day.
WordPress Hacking – Statistical Information
According to many security experts, WordPress hacking activity is on the rise, and many WordPress sites run little to no WordPress security.
The statistics below come from various WordPress security studies conducted by leading website security firms (see “sources” below):
- More than 70% of WordPress installations are vulnerable to hacker attacks.
- 26 million of 36 million self-hosted WordPress sites run little or no security.
- It takes 152 days on average for a webmaster to notice they’ve been hacked.
- The average time to resolve a cyberattack is 32 days.
- There are over 500 WordPress core & plugin exploits.
- Only 15% of webmasters have upgraded to the latest WordPress version.
- 73% of WordPress sites are hacked within 12 months.
- 72% of sites run little or no WordPress security.
- 63% of webmasters don’t know their sites have been hacked
- 42% rise in hacking activity in 1 year.
The above data comes from various sources, including:
- National Vulnerability Database
- WPWhiteSecurity.com
- SecurityAffairs.co
- Trustwave.com
- Stopbadware.org
- BlogDefender.com
Most Website Owners Are Not Aware Their Sites Have Been Hacked
Very few hackers have any reason to advertise the fact that they have broken into someone else’s site …

Most hackers need the resources and reputation of the site they hack into to carry out their criminal activities, and so they have no reason to make their compromised sites obvious. In fact, a lot of effort goes into finding creatives ways to stay “hidden” and go about their business undetected, including programming active bots to turn on and off and continually change their “signature” to avoid detection.
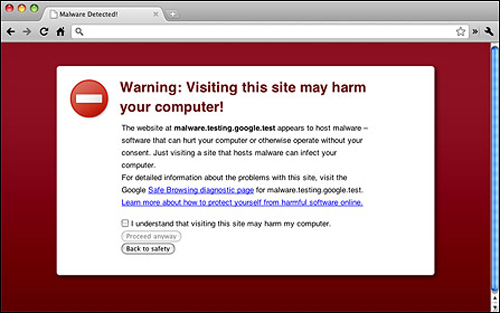
This means that if your site has been hacked and you don’t have a file monitoring system in place, you may not know about it unless your host detects unusual activity on your site and alerts you to this fact (e.g. unusual traffic spikes), or your browser puts up a warning when you try to visit your site …
Most Website Owners Don’t Know How Hackers Got Into Their Sites
According to a report called “Compromised Websites: An Owner’s Perspective“, which is published by security vendor Commtouch and StopBadware, a nonprofit organization that helps webmasters identify, remediate and prevent website compromises, the leading cause of website compromises appears to be outdated content management software (CMS).
And the leading CMS in the world as confirmed by the report is WordPress …

In other words, failure to keep your WordPress site updated can significantly increase your site’s exposure and risk to being hacked, especially if the version you are currently using is found to contain a security weakness that can be exploited by a hacker.
Most Website Owners Don’t Know What Hackers Are Doing With Their Sites
Hackers don’t just target well-known sites with loads of traffic. There are all levels of hackers, from beginners looking for anything they can crack in order to hone and improve their skills, to programs created by expert hackers that will automatically find and take over your site as a simple matter of routine.
Once hackers gain access to your website, they can do all kinds of damage to your site, your data, and your reputation.
For example, they can:
- Implant phishing pages and landing pages deep inside your website and drive visitors to that page (where they will then scam innocent people at your expense)
- Replace your affiliate links with their own
- Harvest mailing lists and databases
- Inject false content into your pages and even your news feeds
- Steal, edit or delete your content
- Destroy your data
- Completely lock you out of your own website
- Etc …
Having your website hacked can lead to emotional distress, significant financial losses from downtime and data theft, and loss of credibility … even potential lawsuits!
Not only is it awful to discover that your website has been hacked, but it can also be severely disheartening to find out that website security is ultimately not your web host’s problem … it’s yours! You are responsible for ensuring that your WordPress site is secure, not your web host (if in doubt, check your web hosting company’s policies).
WordPress Security – There’s No Easy Or Simple Solution
Website security is like an “arms race” … the more you try to secure, protect, and defend your site, the more that hackers will try to devise new methods, strategies, and technologies for attacking your site and getting access to your site’s files and details.
As mentioned before, some hackers belong to vast global criminal networks and have the resources and the funding they need to develop sophisticated destructive and invasive technologies.
The ever-changing nature of online security is a never-ending game of “cat and mouse” played between security experts, web developers, hackers, and malicious users. Like web security in general, WordPress Security is a complex subject comprised of many areas, and keeping up with the latest developments is very difficult. No single resource or company can provide you with “ultimate” security and protection against cybercrime.
![]()
*** IMPORTANT – PLEASE READ ***
As the main objective of WPCompendium.org is to provide WordPress users with practical and easy-to-follow tutorials that do not require technical or coding skills, our WordPress Security training module comprises of basic tutorials about WordPress security only. They will help you understand how to keep your WordPress site secure and protected against many security threats, but not all threats. Online security and website security are vast, complex topics and most of the information on this subject is too technical to fit within the scope of our tutorials.
If you own or manage a WordPress site, you need to treat web security very seriously. Remember that the security of your website is your responsibility.
WordPress Security Tutorials
Go through the tutorials in the WordPress Security training module and make sure to apply all of the basic security measures presented in the tutorials to harden your site, but don’t stop there. Continue to educate yourself about online security threats and keep learning new ways to keep your online assets safe, secure, and protected against hackers, malicious attacks, and security exploits.
Also, make sure to review our free WordPress Security Checklist to ensure that your WordPress site will remain fully protected and secure.
To view and download a printable copy of our free WordPress Security Checklist, go here:
![]()
Remember to always backup your WordPress files and data before making any changes.
Do not ignore WordPress security. If you need help keeping your WordPress site secure and you are not sure what to do, ask a professional WordPress service provider or WordPress security expert for assistance.
WordPress Security Tutorials
WordPress Security Overview

Basic Web Security And Threat Risk Prevention
Your Devices – Computer Security

Your Devices – Software Security
Your WordPress Site – Basic Content Protection
Your WordPress Site – Basic Website Protection
Your WordPress Site – Advanced Content Protection

Your WordPress Site – Advanced Website Protection

***
"I have used the tutorials to teach all of my clients and it has probably never been so easy for everyone to learn WordPress ... Now I don't need to buy all these very expensive video courses that often don't deliver what they promise." - Stefan Wendt, Internet Marketing Success Group