 This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we look at some of the reasons that motivate individuals to hack into computer networks, computers, and websites.
This tutorial is part of our tutorial series on WordPress Security. In this tutorial, we look at some of the reasons that motivate individuals to hack into computer networks, computers, and websites.
***
Understanding The Mindset Of Hackers
As we’ve seen in the overview of our WordPress Security Guide For Beginners, WordPress is a secure platform for websites, but a WordPress site doesn’t exist alone. Overall web security comprises of various components that malicious users can exploit if weaknesses or vulnerabilities are found.
Despite the impression that media reports may give about certain sites being specifically targeted for attack by ‘hacktivists’ pursuing a personal political agenda, very rarely do hackers attack a website for personal reasons. Typically, most hackers will target any website that provides them with opportunities to improve their skills, obtain sensitive information, wreak havoc and disruption on hapless website owners, or where there is some potential for financial gain.
Some computer security industry experts argue that those individuals that we commonly refer to as “hackers” i.e. people who seek to exploit weaknesses in computer systems or computer networks for profit, protest, or challenge, should really be called “crackers” because their main intention is not to “hack” code, but to “crack” into computers and computer networks.
Additionally, it’s important to understand that there are different types of “hackers”, such as:
- White hat – this group of hackers includes computer security experts employed by professional companies to test the security of computer systems
- Black hat – this group epitomizes what we often fear in a computer criminal, and are the people that we referred to as “crackers” above. Black hat hackers violate computer security for malicious purposes or personal gain and often break into secure networks to destroy data or make the network unusable for those who are authorized to use the network.
- Grey hat – this group is a mixture of white and black hat and includes people who surf the net searching for security vulnerabilities in computer systems so they can break into the systems and notify the system administrators of the security vulnerabilities (which they often then offer to fix for a fee).
- Elite – these are highly skilled hackers who have attained a degree of notoriety and social status in the hacking community.
Hackers are by no means limited only to the above categories. Hacker definitions can also range from the brand new and inexperienced neophytes, to script kiddies who use hacking software packages, to blue hat hackers (people who test security systems but are not employed by security companies), hacktivists (people who hack to promote a specific social, ideologic, religious or political message), Nation State hackers (intelligence agencies and cyberwarfare operatives of nation states), and organized criminal gangs, whose sole motivation is to commit cybercrimes for profit.
In this tutorial, we’ll use the word hacker to mean the type of hacker most people generally think of when they think of someone breaking into computers and websites to cause malicious damage with criminal intent …

Regardless of what category a hacker belongs to, they are usually intelligent and inquisitive individuals who typically begin their careers when they are young and have a lot of time on their hands and enjoy the feeling of power that comes with being able to control machines like computers.
Why Hackers Break Into Websites
There are many reasons why hackers break into computer networks, computers, and websites, including:
- Because they can and/or need to satisfy their curiosity or need to feel challenged.
- To improve their hacking skills.
- To gain social status, notoriety or approval from their peers and/or claim bragging rights.
- To obtain or steal sensitive data for personal or financial gain using methods like searching through personal data files, adding malware like keylogging software, etc.
- To use your computer as a way to hack into other people’s computers.
- To wreak havoc on hapless website owners and disrupt people’s lives and businesses.
As a website owner, you should be concerned with the reasons why people would want to gain access to your website.
Just like thieves who break into homes or rob stores, rarely do hackers commit crimes because they hold a personal grudge against the home or store owner. Most of the time, thefts and robberies are opportunistic crimes committed by people seeking cash or home valuables and products from stores that can be easily and quickly traded for cash.
Likewise, hackers seek vulnerable websites that can provide them with opportunities like:
Host Malicious Scripts On Your Server
Hackers who create malicious scripts for distribution need somewhere to host these. They can’t set up sites under their own names as this would give their identity away, so they look for trusted sites where they can upload their scripts.
Redirect Your Visitors To Their Sites
Website owners use files like .htaccess and robot.txt to provide search engines with better indexing for their websites. The robot.txt file, for example, tells search engine robots what they can and can’t index, while the .htaccess file tells search engines how the site should be indexed.
These files, then, instruct search engines to do things like index the entire site, ignore specific parts of the site, or load certain web pages instead of others. By gaining control of your site, a hacker can get search engines to follow their instructions instead of yours.
Steal Your Money
Many sites like niche blogs, etc. use monetization methods like affiliate links, AdSense, banner advertising, etc. By hacking into sites that are monetized using the above methods, hackers can replace affiliate links and Google AdSense publisher IDs with their own, and divert earnings from those websites to their own accounts.
Blackhat SEO
If hackers gain access and control of your site, they can insert keywords and backlinks pointing to their own sites, and attempt to artificially boost their own search engine rankings while simultaneously destroying your site’s reputation in the process.
Comment Spamming
Aside from the problem caused by comment spammers, many hackers exploit commenting features to promote websites that may contain malicious software and infected download files. Often, this kind of spamming is done automatically using software, which makes it overwhelmingly difficult for website owners to manage and keep on top off.
Phishing Scams
Most people nowadays have heard of ‘phishing’ scams, where people are lured to fake websites designed to obtain their personal information, such as usernames, passwords, bank account details, and more.
Hackers can change your DNS (Domain Name System) record information using methods like DNS hijacking, to point visitors to a site designed to imitate the original site. When visitors arrive at the fake site, they are then fooled into trusting the site (depending on how convincing the imitation is and how sophisticated the methods of deception being used are), and enter personal information, which can then be exploited by the hacker.
The above are just some of the reasons why hackers crack websites with security vulnerabilities.
Getting Inside The Mind Of A Professional Hacker
Just as many criminal and forensic investigators try to get ‘into the mind of the perpetrator’ in order to solve their cases, as part of the process of learning how to secure your website, it’s important, therefore, to try and understand how a hacker thinks.
Let’s start then, with the most common methods that hackers will use to try and penetrate your online defenses.
Data Gathering And Analysis
Many hackers begin by trying to understand the underlying web technologies used by your website. This can be done by collecting information about your website’s host and the web technologies installed on your server.
Website Analysis Tools
There are a number of website analysis tools that you can search for information about a website for free.
For example, if you go to a site like www.builtwith.com …

And type in a website address, then click ‘Lookup’ …

You will get a list of all the web technologies used for that website …

(BuiltWith.com)
Another free online tool that is available to anyone who wants to know details about your site such as estimated traffic, server configurations, IP address, name servers, and domain name registration and renewal dates is Who.is …

(Who.is)
AboutUs.org is a meta search engine that gathers information about websites such as company details, website analysis and domain name information from different sources, and presents these details in one combined results page …

(AboutUs.com)
Another useful tool for providing information about websites is Alexa.com …
(Alexa.com)
Alexa provides useful information about sites stored in its huge database of indexed websites like contact details, visitor demographics, and internet traffic stats.
If you want to search for information about a website that is specifically related to the WordPress platform you can use a tool like hackertarget.com …
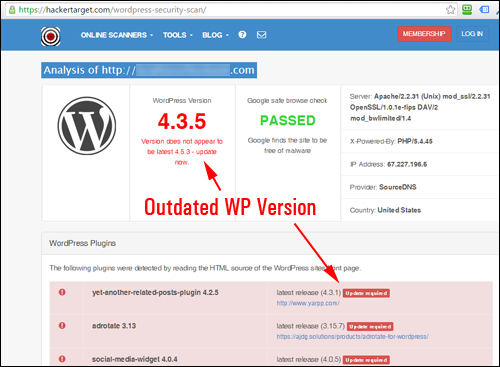
(https://hackertarget.com/wordpress-security-scan)
The above are just some examples of tools that anyone can access and use to gather information about a website’s technology.
Hackers use the above plus a range of other sophisticated software tools, scripts and methods to analyze websites and search for specific technologies with versions containing known security vulnerabilities.
Source Code
Even your own website can divulge important information that could be used by hackers to exploit your site.
For example, if you use Firefox to browse the web, you can easily view any website’s underlying code by selecting Web Developer > Page Source …

The source code for the web page you are viewing will then display on your screen …

By browsing the source code of a web page, hackers can identify what scripts, applications, and programming languages are being used, explore information in hidden fields, and read programmer’s HTML comments.
![]()
Tip: Comments in web page code can make it easier for hackers to understand and reverse engineer your source code. If you plan to get any web development work done on your website, ask your web developer to provide you with a separate document describing the variables, functions and/or methods used, and store this file in a secure offsite location.
Investigative Research
In addition to the above tools, hackers can also use subtle methods, such as examining a website’s cache, which leaves no trail for webmasters to detect in their web analysis tools. This method is explained further below.
Search engines store web pages in caches, as do internet browsers (for example, when the back button is pressed, the local cached version of a page may be displayed instead of a new request being sent to the web server).
Having a cache of your website provide no search engine benefits and gives hackers an opportunity to obtain information about your website. It’s a good idea to remove cached web pages from the Google Index.
To learn how to remove the cached version of a web page from Google, see the article below:
Social Engineering
Another way that hackers can gather data about your website without arousing suspicion is through social engineering.
Essentially, social engineering is when people with malicious or criminal intentions piece together an elaborate lie, con or impersonation based on accurate information gathered from their victims, which they then use to try and deceive, defraud, steal from, or harm the victim and others. These lies can be very hard to spot because they are based on actual, verifiable information about the victim.
As an example, by accepting someone that you don’t know as a new “friend” on Facebook, you could be giving a potential hacker access to personal information about you, such as your partner’s name, how many children you have (and their names and ages), which school you went to, where you live, shop, play sports at, where you regularly go to eat, what you recently bought or traveled to, what you love doing as a hobby, personal details about your family, friends, and so on.
Once a hacker knows some things about you, like your interests, hobbies, the type of work you do, etc. they can then search through other social networks, forums, and web properties to get a better idea of who you are and what you do.
For example, they can visit LinkedIn and get details about your work history, current and past employment or business details, read your resume, etc …
They can also follow you on Twitter and gain an understanding of your social and political views, opinions, affiliations with organizations, current activities, etc… all based on the content of your tweets.
They can visit sites that allow you to search for information about people, like Pipl.com …
And uncover more links on the web about you that allow them to continue building up a profile of who you are …
 All of this information about you that is available on the web can be used by a hacker to falsely impersonate you. They could then request information from your service providers while posing as you (e.g. login or account details, etc) and get access to your web properties, or pose as one of your service providers and entice you to provide them with the additional details they need to hack your website and victimize you.
All of this information about you that is available on the web can be used by a hacker to falsely impersonate you. They could then request information from your service providers while posing as you (e.g. login or account details, etc) and get access to your web properties, or pose as one of your service providers and entice you to provide them with the additional details they need to hack your website and victimize you.
Data Mining
Once a hacker knows what they are looking for, they can use data mining methods to find the information they are looking for and pinpoint ideal target sites to attack.
This can include something as simple as performing advanced search engine queries looking for sites that match specific conditions, or using automated scripts that go out searching for servers that contain known vulnerabilities and potential security leaks.
![]()
Tip: By monitoring your website’s stats, you can identify what search queries visitors are using to find your site, and spot any unusual queries (see below).
Google – A Hacker’s Tool
Google is not only a great search tool for online users, it also allows hackers to perform advanced search queries that can help them identify potential target sites.
Google Site Search Query
For example, you can use the ‘site’ search query shown below to perform advanced searches on Google (note: leave no spaces in the search query) …

Using the ‘site’ operator in your search query returns all the pages that Google has indexed for a specific website …
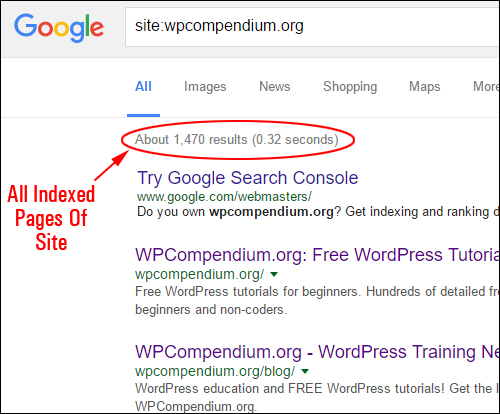
Hackers can use this operator to learn more about your site. For example, they can use it to reverse engineer your site’s file structure.
Google Cache Search Query
Hackers can also examine cached web page URLs, which allows them to work undetected.
To view the cached version of a website or web page, use the operator shown below …

This returns the cached version of the web page you have just searched…
Google Link Search Query
Another operator that is commonly used when studying websites is ‘link’ …

Running a Google search with the ‘link’ operator returns a list of inbound links to a URL (i.e. links pointing to a website from other domains) …

Hackers can also filter down the results of web sites that contain many pages (e.g. an active forum) using multiple keywords.
As an example, consider the search results shown in the example below for a very popular online forum …

Using additional keywords in the search query has significantly reduced the number of results and refined these to very targeted listings for the specific topic being searched …

Now that you understand a little more about how Google’s advanced searches using operators works, how exactly is this useful for hackers?
Well, let’s start with something simple …
Hackers can use advanced search queries to find files in websites that the site owner may not know are exposed, which may contain private data that the site owner never intended to share publicly. This could be a list of customer emails and phone numbers or downloadable files for registered users of that site only.
For example, the site in the screenshot below sells downloadable information products in the form of .pdf files and is potentially losing thousands of dollars in sales, because the owner has not secured their files (i.e. their product), as the search below of their site plus the operator ‘filetype:pdf’ reveals …

Hackers will search for all kinds of files that may contain useful data. These include the following file types …

![]()
Useful tip: Search your own website for any files that may contain sensitive data and get these files protected from public access as soon as possible.
Simply enter the following search query into Google (replace ‘abc’ with the filetype extension, e.g. ‘pdf’, ‘xls’, ‘doc’, etc …)

To learn more about securing downloadable files on your website, see the tutorial below:
Hackers can also use advanced search queries in Google to find websites that have known security vulnerabilities.
For example, let’s say that a potential vulnerability is discovered in an older version of WordPress, e.g. version “3.4.2”.
All a hacker needs to do to find WordPress sites that are still running on the older version is go to Google and type something that is unique to WordPress sites (called a ‘digital footprint’), such as “powered by WordPress” …

And add the version number to the search query …

Hackers can easily automate the above process using software that searches and finds WordPress sites and the versions containing the known security issues, as well as a range of other query strings that helps them quickly identify sites that have no security and are thus easy to target.
To learn how to hide information about your WordPress site like plugins, themes, installation versions, etc., see the tutorial below:
Escalation Of Attack
Once hackers find security vulnerabilities that allow them to gain some kind of access to your system, they will explore your site deeper, looking for weaknesses in your site’s configuration that can be fully exploited. If a hacker is eventually able to bypass your site’s login restrictions and make themselves an administrator, then your site will become fully compromised and be under the hacker’s complete control.
Worse still, there may not be any obvious sign that your site has been compromised. Experienced hackers know how to ‘keep the door open’ so that they can log back in anytime they want to and modify log files to avoid being detected. You could end up running a hacked website without even knowing that someone else is using your site for their own malicious or criminal benefit.
This is why WordPress security is so important and why we recommend going through the tutorials in the WordPress Security module to learn more about how you can keep your WordPress site secure and protected.

(Source: Pixabay)
***
"I have used the tutorials to teach all of my clients and it has probably never been so easy for everyone to learn WordPress ... Now I don't need to buy all these very expensive video courses that often don't deliver what they promise." - Stefan Wendt, Internet Marketing Success Group