 WordPress is the world’s most used content management system making it an obvious target for hackers.
WordPress is the world’s most used content management system making it an obvious target for hackers.
In early 2013 a worldwide brute-force attack began hitting WordPress installations on virtually every web host in existence.
These attacks were caused by computer networks infected with malware and programmed to attack other installations, also commonly known as “botnets”.
How To Protect Your WordPress Site From A Brute-Force Attack
About Brute-Force Attacks
A brute-force attack is a technique used to break an encryption or authentication system by trying all possibilities.
(Source: Chinese University Of Hong Kong)
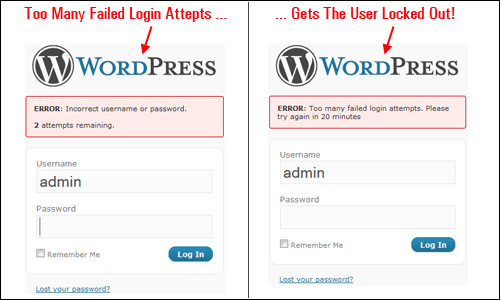
One of the many ways hackers will attempt to break into a WordPress site is by trying to guess the site’s administration login username and password. This can be done using software tools that automatically tries to guess hundreds of possible login combinations in minutes.
If you’re using obvious usernames and weak passwords that are easy to guess, your website could be easily hacked by repeated attempts to work out your site’s login details.
This is called a “brute force” attack.
What Is A Botnet?
A botnet is a number of Internet-connected computers communicating with other similar machines in an effort to complete repetitive tasks and objectives. This can be as mundane as keeping control of an Internet Relay Chat (IRC) channel, or it could be used to send spam email or participate in distributed denial-of-service attacks. The word botnet is a combination of the words robot and network.
(Source: Wikipedia/botnet)
”Botnets” are networks of computers that have been compromised and infected with malicious code or scripts, which can then be controlled remotely as a group, often without the computer owners’ knowledge or awareness.
Botnets are regularly used to blast mass spam emails from computers of compromised user accounts.
The screenshot below was taken from a site that monitors online security showing the locations of the command centers of ZeuS – a botnet that has been actively infecting computer networks all around the globe since 2009 …

(ZeuS is a botnet that has been actively compromising computer networks all around the globe since 2009. Image: SecureList.com)
These were well organized and highly distributed botnet attacks. Over 90,000 IP addresses were identified by a number of hosting companies just in the initial attack, when the web was flooded with millions of attempts to force their way into WordPress user admin areas. The large-scale attack then continued, with over 30,000 WordPress blogs being hacked per day.
Coverage of this brute-force botnet attack was reported by all the major webhosting companies, as well as the leading technology publications, such as TechNews Daily, Forbes, PC Magazine, BBC News, Tech Crunch, and even on the official website of the US Department of Homeland Security …
(Powering millions of websites and blogs worldwide makes WordPress a target for hacking attacks)
Does This Mean We Should Stop Using WordPress?
No. In fact, there are lots of very good reasons why you should choose WordPress if you are concerned at all about the security of your web presence.
We explain why WordPress is a secure platform for websites in this article: Are Open Source CMS Platforms Like WordPress Secure?
![]()
It’s important to note that, in the case of the mass brute-force attack described above, there was actually no WordPress vulnerability being exploited (the same script was also targeting sites built using platforms like Joomla).
Mike Little, the co-founder of WordPress, said this about the brute-force attacks:
It is a “simple” script that attempts to login using the admin login and a generated password. So if your password is too short or based on dictionary words it will be guessed and then the script can login legitimately and do whatever it wants including installing scripts (as plugins) or editing files. The attack tries to guess your password, if it succeeds, the most secure site in the world is wide open because they have your password.
How To Protect Your WordPress Blog From Being Brute-Force Attacked – Ten Security Checks
Every web site with a vulnerability provides an opportunity to hackers. A compromised blog offers hackers with a platform for distributed denial of service (DDoS) attacks, spreading malware and engaging in information theft.
If a hacker can discover a security flaw, the website can then be used to attack other highly-valued web sites.
Additional undesirable impacts of being hacked and your site security compromised include getting blacklisted by search engines, having spammy links advertising things like gambling, discounted fashion, etc. in your content, redirecting visitors to phishing sites or other websites, data exfiltration (stealing customer details or Personal Identifiable Information from your web applications), and lots of other nasties.
The truth is that malicious bots are looking for security exploits and trying to hack into your web site as you are reading this at this very moment. Whether they will hack in successfully depends on how hard or easy you have made things for hackers or bots to continue persisting until they can work out a way to get access, or give up and go look for an easier target.
How Much Information About Your WordPress Site Are You Broadcasting To Hackers?
Does your website run on WordPress? If so visit a site like Hackertarget.com and run your site through their WordPress security check …
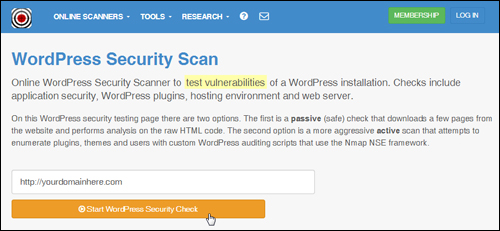 (WP Security Check Product image source: Hackertarget.com)
(WP Security Check Product image source: Hackertarget.com)
You will see that the scan returns a number of results and information about your website setup …

(WordPress security check results. Image source: Hackertarget.com)
It should be obvious after using the tool shown above that if you are able to freely access all of this information about your WordPress website, then hackers can too.
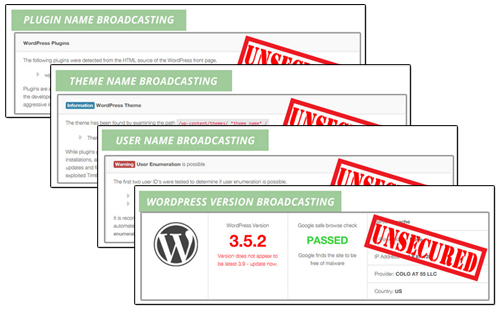 (Screenshot image: BlogDefender site)
(Screenshot image: BlogDefender site)
Being able to see which version of WordPress you are using, which plugins and themes you have installed on your site, and which files have been uploaded to certain directories on your server are all valuable information to hackers, as this informs them about any exploitable security vulnerabilities, especially in older versions.
If your site or blog is driven by WordPress and you’re not taking appropriate steps to toughen up your site, then we can practically guarantee that, at some time in the near future, your site will be hacked, or at least targeted by bots, because these brute-force attacks are systematically targeting WordPress installations around the world!
Whenever a website is hacked, webmasters can find themselves completely “locked out” of their own site, or notice that their files have been vandalized or even that their content has been completely wiped out. Typically, sites will become infected with malicious scripts without the owner’s knowledge or awareness.
To help avoid the heartache (and potential financial loss) that comes with discovering that your website has been hacked into, we have listed below 10 simple, yet essential and effective security checks that will help to protect your WordPress site from being attacked by brute force botnet hacking attempts.
![]()
Note: Some of the recommended measures below need some technical skills to modify core WordPress and server files. If you are not technical-minded, or don’t want to mess around with code on your site, then ask your web host or search for a WordPress service provider in our WordPress Services Directory.
***
Security Measure #1 – Contact Your Hosting Provider
Contact your hosting company and ask them what security systems have been put into place to protect your site from brute force attacks, and what they are doing to make sure that your server files and data get backed up.
Make sure that your hosting service provider regularly backs up your server files and that, if anything should happen, you can quickly and easily get your site back.
Security Measure #2 – Perform Full WordPress Backups And Keep Your Website Frequently Updated
Never rely on your webhosting company for site backups. Instead, learn how to maintain your WordPress site or pay someone to get this service done for you and maintain a habit of religiously performing a complete WordPress site maintenance routine frequently (e.g. weekly, fortnightly, etc …)
A full WordPress maintenance routine ensures that:
- All unnecessary data and files are removed,
- All WP data and files are free of errors, optimized and backed up,
- All WordPress plugins, themes and software components are up-to-date,
- etc …
A proper WordPress site maintenance routine looks like this …
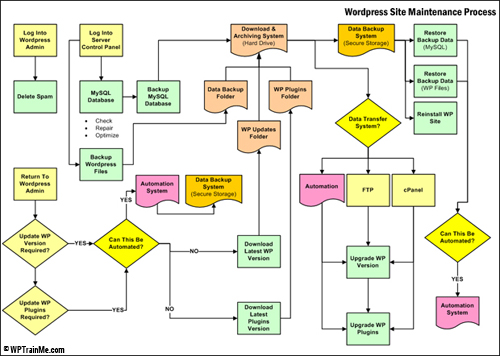 (Maintaining your WP website frequently backed up and up-to-date is vitally important for WordPress security. Source: WPTrainMe.com)
(Maintaining your WP website frequently backed up and up-to-date is vitally important for WordPress security. Source: WPTrainMe.com)
Again, we cannot stress enough how important maintaining your WordPress website fully backed up and updated is. WP maintenance is not hard to do or time-consuming, but it must be done to ensure the security of your website or blog. If you don’t want to learn how to do WP site maintenance yourself, get someone else to do it but make sure it gets done. Backing up your site is the second most important thing you must do after making sure that you are still breathing!
If you don’t want to perform manual backups, there are a number of free and paid WordPress plugins you can use. Learn about a WordPress backup plugin that can automate your backup process here: Backup, Copy & Protect Your WP Site With Backup Creator WP Plugin
Security Measure #3 – Do Not Use “Admin” As A Username
The large scale brute force botnet attack on WordPress sites was mostly an attempt to compromise website admin panels and gain access to the site by exploiting sites with “admin” as their account name.
For reasons of website security, don’t set up sites with the username admin. This is the first thing hackers will test. If your blog’s user name is admin, change it immediately.
For a step-by-step tutorial for non-technical WP admin users on how to change your username, go here: Changing Your WordPress Admin User Name To A More Secure Username
Security Measure #4 – Use A Strong Password
A “brute force” attack occurs when a malicious script continually and persistently hits a login or password field with different character strings trying to guess the right login combination that will give them entry to your site.
Unless some measure is put into place to prevent the brute force attack from happening (see further below for a couple of effective suggestions for doing this), the “bot” will just persist in attacking your site until it eventually gets access.
Weak passwords, therefore, make very easy targets for brute-force attacks. Make sure that you change your password to something that contains at least 8 or 9 characters long, and that includes upper and lowercase letters, combined with “special” characters (e.g. %, #, &, etc).
![]()
If you have trouble coming up with strong passwords or are reluctant to set up different passwords for all of your online logins, then use a password management software tool like Roboform …
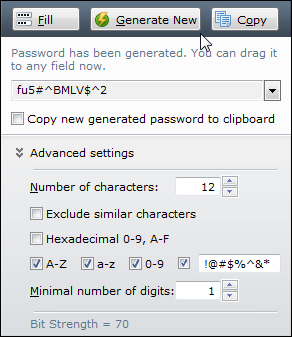 (You can use a password management software tool like Roboform to help you generate passwords)
(You can use a password management software tool like Roboform to help you generate passwords)
We have created a simple tutorial created especially for non-technical WP admin users that shows you how to change your login password here: Changing Your Password In WordPress
Security Measure #5 – Prevent Your wp-config.php File From Being Accessed
The wp-config.php file allows WordPress to communicate with the database to store and retrieve data and is used to define advanced WordPress options.
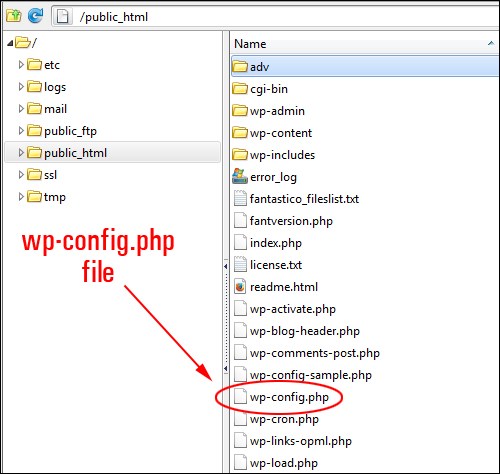
(wp-config.php)
If hackers break into your website, they will typically search for the wp-config.php file, because this file contains your WordPress database details, security keys, etc. Getting access to this information would allow a hacker to change anything in your database, create a user account, upload files and take control of your site.
To protect your WordPress site from being attacked and even being used as part of a bot net, therefore, you must prevent your wp-config.php file from being easily accessed. This requires knowing how to edit database information, move files around in your server and changing access permissions.
Security Measure #6 – Rename Or Delete Unnecessary Website Installation Files
Delete or rename the install.php, upgrade.php and readme.html files from your server.
These files can be removed after installation. If you don’t want to remove these files, just rename them.
Security Measure #7 – Keep Your WordPress Installation, Plugins And Themes Up-To-Date
Hackers are always on the lookout for vulnerabilities in outdated versions of WordPress that can be exploited, including outdated versions of plugins and themes.
Ensure that all of your installation files, plugins, themes, etc. are always up to date.
Security Measure #8 – Disable Your WordPress Theme Editor
WordPress installations come with a built-in editor that allows the administrator to edit theme and plugin files from the dashboard.
In WordPress, you can access the WordPress Theme Editor by selecting Appearance > Editor in the dashboard menu …
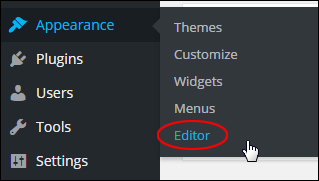
(Accessing the WordPress theme editor using the admin menu)
This allows anyone accessing your blog to view and edit your WordPress theme template files, or cause havoc on your site.
If you want to prevent unauthorized people from accessing the WordPress Theme editor, you will need to disable it. This can be done by adding code to your wp-config.php file.
Security Measure #9 – Remove Access To The Site’s Uploads Directory
The “uploads” directory stores all the media that gets uploaded to your blog.
Normally, this folder is visible to anyone online. All a person needs to do to see all of the contents stored in your site’s “uploads” directory is visit the directory using their web browser …
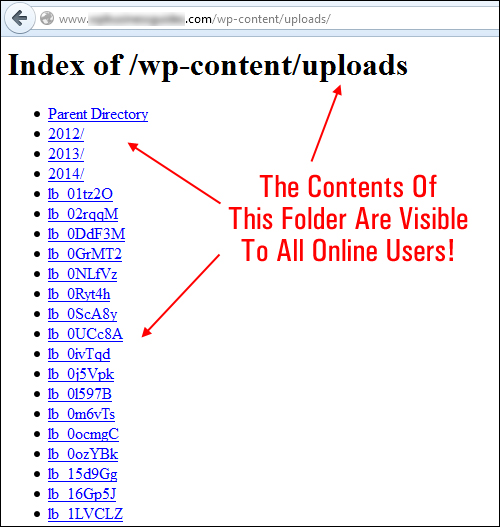
(WordPress uploads folder)
If any directories in your website have weaknesses or vulnerabilities that can be exploited by malicious users, this can threaten the security of your website.
Protecting your directories will prevent unauthorized people from viewing your ‘uploads’ folder and other important directories. This can be done using plugins, setting file permissions, uploading a blank index.php file (this is literally an empty file called “index.php”) to your uploads directory, and so on. Again, it’s best to seek professional help if you are unsure about what to do.
Security Measure #10 – WordPress Security Plugins
Several WordPress security plugins are available that specifically address many common security issues WordPress website owners face, such as preventing unauthorized users from accessing your site, protecting your website from malicious scripts, preventing unauthorized file uploads, etc.
Most WordPress plugins address some but not all areas of WordPress security. One security plugin that seems to do a comprehensive job of scanning, fixing and preventing potential issues that could lead to hackers accessing your site files and causing irreparable damage to your site is SecureScanPro.
(SecureScanPro – WP complete security software)
SecureScanPro is easy to install and easy to use, and fixes most of the security areas that WordPress users need to address.
Another security plugin you may want to consider using is BlogDefender.
Blog Defender Security Product Suite For WordPress
 (Blog Defender WordPress Security Solution)
(Blog Defender WordPress Security Solution)
This product is a package of WordPress security video tutorials, plugins and tools, plus WordPress security documentation in PDF and DOC formats.
BlogDefender shows you where potential security weaknesses in your WordPress installation are …
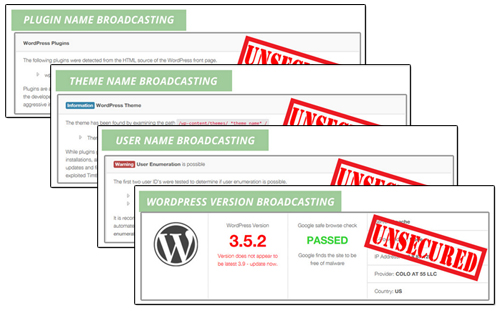 And lets you fix these quickly, easily and inexpensively …
And lets you fix these quickly, easily and inexpensively …
 If you don’t want to invest in a premium security plugin like SecureScanPro or BlogDefender, you can use various free plugins, such as Limit Login Attempts …
If you don’t want to invest in a premium security plugin like SecureScanPro or BlogDefender, you can use various free plugins, such as Limit Login Attempts …
WordPress is a secure web platform, but neglecting essential maintenance tasks like updating your WordPress software, plugins and themes, tightening file and data security and taking other necessary precautions can expose your site to malicious by hackers and bots.
Regardless of the type of business you run or plan to run online and how small you think your web presence is, you cannot ignore the importance of securing your website or blog.
As a final reminder, below is the advice given by an expert on web security to all WordPress users following the global brute force attacks by botnets on WordPress in 2013 …
Owners of websites based on WordPress CMS must improve at least basic security settings and implement best practices such as the use of robust passwords and the accurate management of “admin” accounts.
Pierluigi Paganini, Chief Information Security Officer, Security Affairs
***
As you can see, website security is very important if you run a WordPress site. Hopefully, the information in this article will help prevent brute force attacks on your WordPress site. If you need any further help or assistance with WordPress security, please seek help from a WordPress security specialist, or search for a professional WordPress technical provider in our WordPress Services Directory.
Also, do yourself a favor and subscribe to WPCompendium.org to receive notifications via email whenever we publish new articles and tutorials on WordPress security and reviews of new WordPress security plugins and solutions.
***
"These tutorials have so much information and are easy to understand. If you use WordPress or plan to in the future these will help you with everything you need to know." - Valisa (Mesa, Arizona)
***

